Features
‘We weren’t wild. We were unprotected’: A generation groomed and forgotten

Trigger warning: This article contains graphic references to child sexual abuse, grooming, and trauma.
WE were the first kids online. Dial-up tones. MSN Messenger. Webcams balanced on bulky monitors. No rules. No warnings. No one watching.
And the predators? They found us before our parents even knew what a USB was.
It started in the chatrooms. Kids Chat. AOL. Yahoo. We’d log in at nine, say we were fourteen, and within minutes we were being asked:
“What are you wearing?”
“You’re cute.”
“Show me.”
They showed themselves too. Full-grown men — not eighteen, not twenty-one — men in their thirties, forties, sixties. They told us we were special. Mature. Beautiful. And we believed them — because nobody told us not to.
It became normal
It didn’t feel like grooming. It felt like attention. Excitement. Thrill. Fear. Shame. All tangled together in a way that still knots up in my chest to this day.
We started meeting them. Men with cars. Men with drinks. We lied about our ages, because that’s what girls did. We said we were sixteen when we were thirteen.
But the truth? We looked ten. And they knew it.
We thought we loved it. That’s what they made us believe. That wasn’t informed consent — that was childhood confusion weaponised.
It became so normal it was daily. The damage was done before we even knew we were bleeding.
He could’ve killed me
He was “Ben” (Not his real name).
He was much older Asian man. We’d seen him once, walking home. He offered a lift. There were a few of us, so we got in. Young. Naïve. Stupid. But kids.
The next time, I went alone.
He picked me up. Drove me to a secluded spot — dark, empty, silent. My gut screamed. Everything in me said run. But I was trapped in his car.
He leaned in. Tried to kiss me. Grabbed at me. Pressured me. His hands. His breath. His force.
I froze. So I lied.
Pretended my sister was calling. Faked a conversation. Loudly said where I was — just in case. He hesitated. Maybe it scared him. Maybe it didn’t. But he drove me home.
The moment we hit my estate, I opened that door before the car even stopped and ran like hell.
Because I truly believed — if I hadn’t — he’d have raped me. Or worse.
Twenty men. Two girls. No way out
J said she knew them.
“They’re alright,” she said. “It’s fine.”
They were foreign men. They picked us up — two teenage girls — and took us to a house.
When we walked in?
More than twenty men. All older. All staring.
Something was wrong. The air was heavy. We were offered drinks. I told J not to take it. She did anyway.
Then we were on the move again — to another house, just the two original men now. We followed, confused. Upstairs. Into a bedroom.
It became clear, fast.
This wasn’t a hangout. This was a setup.
I grabbed J’s arm and said, “We’re going.”
We ran. Pushed past the men. Jumped over them on the stairs. Flew out the door and didn’t stop.
We called two older guys we knew — the only people we could think of.
They picked us up. Got us out of there.
It was over. But it never really was.
Because we were just kids. And it had become normal to be in danger.
They said we were naughty girls
I once tried to speak out. I’d had enough. I cracked. I told someone. And they didn’t believe me. Worse — they blamed me.
I was unstable. Dramatic.
“You loved the attention.”
“It’s your fault.”
“You were asking for it.”
Even now, when I talk to girls I grew up with, they ask:
“Was it really grooming?”
“We were naughty, weren’t we?”
“Did that really happen to us?”
Yes. Yes, it did.
That is the sound of an entire generation gaslit by silence.
We were groomed — online and offline — while every adult in the system looked away.
What the system never saw — because it wasn’t looking
There were no safeguarding policies for what we lived through. No assemblies warning us about “online predators.” No teachers trained in grooming recognition. No systems prepared for what the internet was unleashing.
We were the first generation to be groomed through a screen. And the institutions that were meant to protect us? They were still warning us about strangers with sweets in vans.
While we were being exploited by men in our inboxes, schools were still showing us cartoon leaflets about “saying no to drugs.” Police didn’t know what screenshots were. Social workers weren’t trained in digital abuse. And the law? It barely existed.
The internet was a playground — but predators were the only ones who read the rules.
The internet grew — but protection didn’t
By the time adults caught up, the damage was done. We weren’t seen as victims — we were labelled problems.
Disruptive. Promiscuous. Attention-seeking.
Our trauma was punished. Not supported. Not believed. Not understood.
They didn’t ask why we were spiralling. They gave us detentions, suspensions, isolation rooms. They moved us from school to school. They called our parents in. But they never called out the men messaging us at midnight.
We were never asked the right questions
Nobody said:
“Are you okay?”
“Do you feel safe online?”
“Has anyone ever made you uncomfortable in a chatroom?”
We were never taught that being manipulated by a 35-year-old man wasn’t our fault. Instead, we were told to be careful — like we were the problem.
And we internalised that.
For years, we thought we were “naughty.” We laughed it off. We carried the shame. We blamed ourselves — and each other.
But we weren’t being difficult. We were being groomed. And nobody. Ever. Asked.
The legacy we still carry
It didn’t end when the messages stopped. Or when the house door shut. Or when the man drove away.
It stayed with us.
In our nervous systems. In our relationships. In our sense of safety. In the way we second-guess ourselves, even now.
We survived the grooming. But nobody prepared us for the aftermath.
We grew up — but the damage grew with us
The world taught us that what happened to us wasn’t that serious. So we learned to swallow it.
We carried trauma into our teens. Into sex. Into adulthood. Into breakdowns and addiction. Into trust issues and triggered silences. Into: “Why can’t I just get over it?”
And still — it’s rare anyone names it for what it was.
Because we didn’t get groomed today, with safeguarding policies and public outrage. We got groomed back then — in the wild west of the internet, when people thought it was just “girls being flirty.”
No one saw us as victims. So we didn’t know we were.
Even now, we doubt ourselves
That’s the legacy. Not just trauma — but doubt.
We still hear the voices in our heads:
“Was it really that bad?”
“We went along with it, didn’t we?”
“We lied about our age though…”
We repeat the lies we were fed. We laugh when we talk about it, because we don’t know what else to do. We swap horror stories like they’re throwaway memories.
But deep down? We know we weren’t wild. We were unprotected.
And that’s what hurts the most — that we’ve had to live this long wondering if we did this to ourselves.
We didn’t.
This never stopped — it just got easier
Predators didn’t disappear when the dial-up tone died. They evolved — just like the tech did.
Now they don’t need to lurk in AOL chatrooms. They’re on Snapchat. TikTok. Discord. Instagram. Fake names. Disappearing messages. Private servers.
They don’t have to ask for your number. They can reach a 12-year-old from a stranger’s story share or a mutual follow.
They don’t have to drive around looking for vulnerable girls. They scroll for them. They search hashtags like “lonely.” They read comments under selfies.
And the difference now? It’s faster. It’s smarter. It’s constant.
And still — the system hasn’t caught up.
They still count on silence
Grooming follows the same steps it always did:
- Spot the vulnerability
- Build trust
- Create shame
- Exploit silence
- Count on institutions to do nothing
Because that’s what still happens today.
A child discloses abuse? They’re asked what they were wearing. How many people they’d slept with. Whether they were “mature for their age.”
The same grooming culture we lived through — is still being handled with the same doubt, denial, and delay.
The system learns nothing
We’ve had inquiries. We’ve had safeguarding scandals. We’ve had high-profile convictions and public horror.
And yet:
- Police still dismiss “difficult” victims
- Schools still prioritise reputation over protection
- The CPS still drops cases citing “credibility”
- Children are still moved while abusers stay put
We’re still here. Screaming the same things we tried to say twenty years ago — and still being told we’re “complicating things.”
We’re done being quiet — and we’re not asking anymore
We’re not confused anymore. We’re not wondering if it “counts.” We’re not searching for the right words to make it palatable.
We know what it was. It was grooming. Abuse. Neglect. Silence. And it wasn’t our fault.
You don’t get to blame children for being vulnerable. You don’t get to excuse grown men who target trauma. And you definitely don’t get to call it a “failure” when the system was built to look the other way.
This is our reckoning
We’re not asking for awareness. We’re done trying to make this easy to hear. We’re not tiptoeing around reputation or waiting for permission.
We are naming names. We are connecting patterns. We are exposing the blueprint.
This is not a call for more safeguarding leaflets or carefully worded apologies. This is a demand:
Acknowledge us. Protect the next generation. And stop pretending this wasn’t by design.
by Sophie Lewis
Author’s Note:
These events are real and happened in South Wales. If this feels familiar — you’re not alone. Your story matters. Even if you’ve never spoken it out loud. Especially if no one ever believed you.
It was real. It happened. And it wasn’t your fault.
If you’ve been affected by the issues in this article
Help and support are available. You are not alone.
Support services in Wales:
- The Survivors Trust – Offers confidential support for survivors of sexual violence
📞 08088 010 818
🌐 www.thesurvivorstrust.org - Rape Crisis England & Wales – Freephone national helpline
📞 0808 500 2222 (12:00pm–2:30pm, 7:00pm–9:30pm every day)
🌐 www.rapecrisis.org.uk - NSPCC (for children and young people)
📞 0800 1111 (Childline – free and confidential)
🌐 www.childline.org.uk - Live Fear Free (Wales) – Support for anyone affected by domestic abuse, sexual violence or violence against women
📞 0808 80 10 800 (24/7 helpline)
🌐 www.livefearfree.gov.wales - BAWSO – Specialist support for Black and minority ethnic communities in Wales
📞 0800 731 8147
🌐 www.bawso.org.uk
Features
Simple home DIY projects

Transforming your living space doesn’t require a professional contractor or an enormous budget. With a few basic tools, some creativity, and a weekend to spare, you can tackle simple home DIY projects that will breathe new life into your home. Whether you’re a seasoned DIY enthusiast or picking up a paintbrush for the first time, these accessible projects will help you personalise your space whilst building your confidence and skills.
Refresh your walls with a fresh coat of paint
One of the most cost-effective ways to transform any room is with paint. A fresh colour can completely change the mood and perception of a space. Before you begin, invest time in proper preparation: clean your walls, fill any holes or cracks with filler, and sand smooth once dry. Use painter’s tape to protect skirting boards, door frames, and ceilings. Choose quality paint and the right finish for your room – matt for ceilings, vinyl silk for kitchens and bathrooms where moisture resistance matters. Don’t rush the process; two thin coats always look better than one thick, drippy application.
Install floating shelves for extra storage
Floating shelves offer both functionality and style, making them perfect for displaying books, plants, or decorative items. The beauty of this project lies in its versatility – you can install them in virtually any room. Measure carefully and use a spirit level to ensure your shelves are perfectly horizontal. Locate wall studs for the most secure installation, or use appropriate wall plugs for plasterboard. Start with one or two shelves to build your confidence before creating an entire display wall. This project typically takes just an afternoon but delivers long-lasting storage solutions.
Create a feature wall with wallpaper or panelling
Feature walls have remained popular for good reason – they add character without overwhelming a space. Wallpaper has evolved tremendously, with peel-and-stick options making installation remarkably straightforward for beginners. Choose one wall as your focal point, typically the wall you see when entering the room. For a more textured approach, consider installing a wood slat wall panel to add depth and architectural interest. This creates a sophisticated, modern look that works beautifully in living rooms or bedrooms. Whichever option you choose, a feature wall can be completed in a single day and makes a dramatic impact.
Update cabinet hardware for an instant kitchen refresh
If a full kitchen renovation isn’t in your budget, replacing cabinet handles and knobs delivers remarkable results for minimal investment. This simple swap can modernise dated cabinets and completely change your kitchen’s aesthetic. Measure your existing hardware’s spacing before purchasing replacements to ensure proper fit. Choose a finish that complements your kitchen’s style – brushed brass for warmth, matte black for contemporary spaces, or polished chrome for classic appeal. You’ll need only a screwdriver for this project, making it perfect for absolute beginners.
Build a simple herb garden
Even without outdoor space, you can create a thriving herb garden on a sunny windowsill. Purchase small terracotta pots, quality potting compost, and herb plants or seeds from your local garden centre. Basil, mint, parsley, and chives are particularly forgiving for novice gardeners. Drill drainage holes if your pots don’t have them, and place saucers underneath to protect surfaces. Not only does this project bring life into your kitchen, but you’ll also enjoy fresh herbs for cooking. It’s a rewarding project that continues giving long after completion.
Upgrade your lighting fixtures
Lighting dramatically affects ambience, yet many people overlook its potential. Swapping outdated light fixtures for modern alternatives can transform a room’s entire feel. Before beginning any electrical work, always turn off power at the consumer unit and verify it’s off using a voltage tester. If you’re uncomfortable working with electrics, hire a qualified electrician – safety always comes first. For those confident with basic electrical work, replacing a pendant light or wall sconce is straightforward and makes an impressive difference.
Final thoughts
These simple home DIY projects prove that transforming your space doesn’t require expert skills or substantial budgets. Start with projects matching your comfort level, invest in quality tools that you’ll use repeatedly, and don’t fear making mistakes – they’re part of the learning process. As your confidence grows, you’ll find yourself tackling increasingly ambitious projects. The satisfaction of creating something with your own hands, tailored precisely to your taste, makes every moment spent worthwhile. Your home should reflect your personality, and these accessible DIY projects help you achieve exactly that.
Features
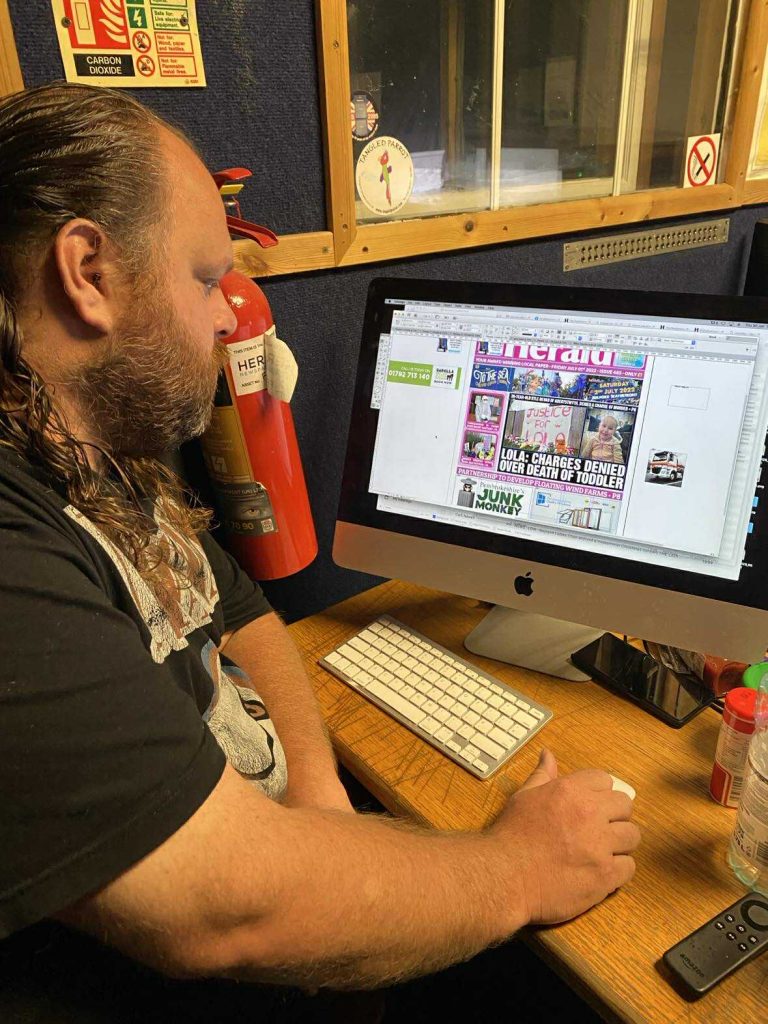
Revolution in the rough: how the Pembrokeshire Herald shook up local news

A rogue wave in quiet waters
ON a grey July morning in 2013, a small team of reporters gathered a makeshift office Milford Haven’s Hamilton Terrace. The air smelled of ink, takeaway coffee, and fresh ambition. Outside, the docks shimmered with summer drizzle; tankers groaned in the estuary, a reminder that Pembrokeshire’s fortunes were often tethered to industries bigger than itself.
Inside, though, another tide was turning. That morning, the first edition of The Pembrokeshire Herald rolled off the presses and onto newsstands across the county.

It was a gamble few thought wise. Regional journalism across the UK was collapsing. Newsrooms were closing at a rate of one a week. Advertising revenues had dried up, circulation was plummeting, and Wales was hit especially hard. Even the venerable Western Telegraph, with its 150-year pedigree and corporate backing, looked nervous.
And yet, the Herald sold out. Locals queued at corner shops and petrol stations to grab a copy. For £1, readers were promised something rare: a paper that would be theirs—unafraid, unfiltered, and unpolished.
Twelve years on, as the Herald breaks digital records with more than 14 million views in a single month, its story is one of survival, reinvention, and disruption. From council scandals to choir fundraisers, it has not only chronicled Pembrokeshire—it has changed how the county sees itself.
The rebel launch
The Herald’s beginnings were almost cinematic.
“Everyone thought we were mad,” recalls founding editor Thomas Sinclair, still at the helm today. “Papers were dying all around us, and here we were launching another one. But we believed Pembrokeshire deserved something better—something that didn’t just recycle press releases.”
The first issue carried stories that cut against the grain: a scathing piece on county hall overspending, a photo-led feature on lifeboat volunteers, and letters from readers who felt ignored by the established media.

The ethos was simple: be the people’s paper. If a farmer in Crymych was angry about planning rules, or a pub landlord in Tenby had a gripe about business rates, they would find their voices printed alongside reports of Senedd debates and crime in Haverfordwest.
Within weeks, the Herald was shifting around 10,000 copies a week. For a county of just over 120,000 people, that was remarkable. Its early success rattled the Western Telegraph, which had long enjoyed unchallenged dominance.
By 2014, emboldened by sales, the Herald launched sister titles in Carmarthenshire and Ceredigion, signalling it wasn’t content with being a local irritant—it wanted to redefine journalism across West Wales.
Grit, growth, and grudges

The mid-2010s were the Herald’s golden years. Circulation climbed, digital traffic surged, and the paper became a lightning rod for controversy.
One of the fiercest battles came in 2016, when the Herald’s bold marketing—claiming it had overtaken the Western Telegraph in reach—provoked a furious response. The Telegraph’s parent company complained to the Advertising Standards Authority (ASA), demanding the Herald prove its numbers.

Twice the ASA dismissed the complaints. “It was classic David versus Goliath,” Sinclair remembers. “They couldn’t stand that we were growing.”
The feud only raised the Herald’s profile. It doubled down on innovation: live-streaming council meetings, experimenting with podcasts, and even testing a radio station. Readers flocked to its coverage of issues like youth unemployment, mental health crises, and planning rows that reverberated from village halls to the Senedd floor.
But controversy was never far away.
- In 2013, an obscene advert accidentally slipped into print, sparking outrage—and free publicity.
- In 2017, Sinclair himself was fined for breaching reporting restrictions in a sensitive case. Critics crowed, but supporters saw it as proof of a paper pushing boundaries.
“The Herald was messy, sometimes chaotic,” says one former reporter. “But it was alive in a way local journalism hadn’t been in years.”

The abyss
In October 2019, the wave almost broke.
The Herald’s parent company collapsed under the weight of spiralling print costs and a botched investment, shuttering three titles and threatening 24 jobs.
“It was devastating,” Sinclair admits. “We’d built something people believed in, and suddenly it was gone.”
Forums filled with laments. One commenter wrote: “Without the Herald, who’s going to ask the awkward questions?”
For Pembrokeshire—where 26% of residents are over 65 and rural isolation makes local news more than a luxury—the loss felt existential.
Salvation came unexpectedly. A Spanish print and media firm, Richographic España, swooped in with emergency funding. The Herald returned, leaner and chastened, but alive.
The scare revealed a hard truth: independent journalism is fragile. Without it, who holds local power to account?
The digital dawn
The near-death experience forced reinvention.
By 2023, with print costs unsustainable, the Herald made a radical move: it scrapped print altogether, pivoting to a free weekly 128-page digital edition.
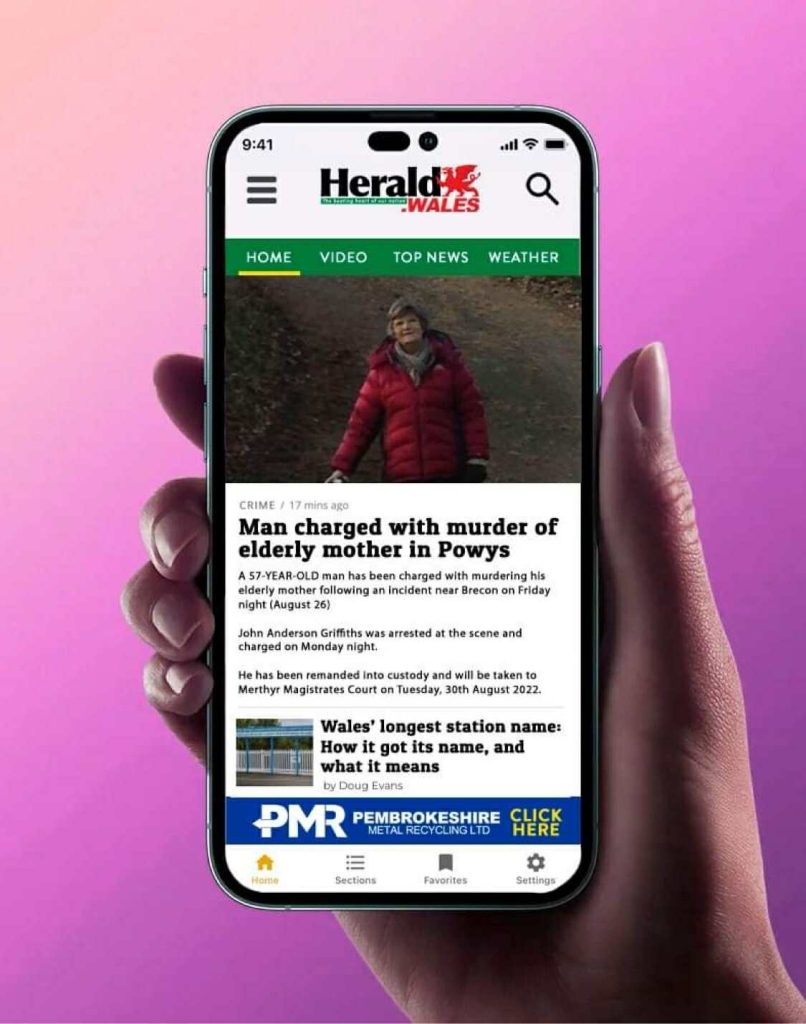
The gamble paid off. The first e-edition was downloaded more than 100,000 times. With clickable ads, instant shares, and no paywalls, it reached corners of the county that had never picked up a paper copy.
Traffic exploded. Facebook followers climbed past 51,000 (overtaking the Western Telegraph’s 47,000), monthly web uniques hit half a million, and social engagement dwarfed that of rivals.
The Herald’s new strength was speed. While the Telegraph often waited to polish features, the Herald broke stories first:
- Avian flu detected near Roch.
- Military flyovers during Russian naval manoeuvres off the coast.
- RAAC concrete crises threatening local schools.
On X (formerly Twitter), users hailed it as the go-to for “what’s actually happening.”
Rivalry rekindled
For more than a century, the Western Telegraph had been unchallenged. But the Herald’s swagger forced it to adapt.
That 2016 ASA spat was only the tip of the iceberg. The real battle was for hearts and eyeballs.
The Herald won them with raw immediacy. Viral stories of goats invading a churchyard or choirs raising money for cancer care travelled faster than any polished Telegraph feature.

Locals noticed. “The Herald feels like us—raw and real,” tweeted one user after coverage of council budget cuts.
Competition sharpened the entire ecosystem. With two strong voices jostling, Pembrokeshire readers got more scrutiny, more coverage, and more choice.
The Herald effect — building pride
If the Herald earned its reputation by ruffling feathers, it cemented its value by lifting spirits. Alongside exposes and political spats, the paper has consistently championed Pembrokeshire’s brighter side.
When the Ty Newydd pub in Dinas Cross faced closure in 2023, Herald coverage helped galvanise more than 200 locals into raising the cash to save it. “Inspiring local journalism at its best,” one X user wrote as the victory went viral.

Schools, too, have felt the Herald’s boost. Milford Haven School’s Gold Calon Y Gymuned award for family engagement in July 2023 was splashed across its pages, with headteacher Sara Davies crediting the coverage for “putting community success on the map.” A year later, the Herald’s GCSE features turned dry exam stats into proud family moments, with parents flooding its comments section to thank it for spotlighting their children.

The paper’s business coverage often becomes a loop of positivity. In 2024, when hardware stalwarts W.B. Griffiths & Son scooped a £2,000 Pembs Lottery prize, they pledged it to local projects — citing the Herald’s years of community coverage as a key motivator. “It keeps us connected,” the owners said.
And when Pembrokeshire County Council secured the insport Gold Standard for inclusive sport, Disability Sport Wales hailed it as a “remarkable milestone” — and locals praised the Herald for making it front-page news.
These moments reveal something the numbers alone can’t: that the Herald is more than a scrappy watchdog. It’s also a mirror of community pride, amplifying joy as fiercely as it scrutinises power.
The global lens
Perhaps the most surprising twist in the Herald’s evolution has come since its digital relaunch: the paper is no longer just Pembrokeshire’s chronicler. Increasingly, it is a bridge between the local and the global.

Take the Jaguar Land Rover cyber-attack in September 2025. The story was everywhere—production halted at JLR’s UK plants, suppliers fearing collapse, the UK government stepping in with a £1.5 billion loan. National headlines framed it as a crisis for British industry.
The Herald’s version? A piece titled “JLR cyber-attack sparks fears for Welsh supply chain”. Within hours of the news breaking, Sinclair had tied the story to ZF Automotive in Pontypool, a Welsh supplier employing dozens and recently backed by Welsh Government cash. The message was clear: what happens in Solihull or Delhi could hit Wales next.

A few days earlier, the Herald had run multiple articles on the Charlie Kirk shooting in the US. Where national media focused on America’s gun politics, the Herald made it resonate in Wales: local MSs Samuel Kurtz and Darren Millar linked the killing to free speech debates in Welsh universities, even pushing for a Senedd tribute.
This is the new Herald playbook: start global, end local.
- Bank closures in Haverfordwest become part of Chinese state media coverage on UK economic decline.
- Ukraine aid debates turn into stories about how sanctions hit Welsh farmers.
- US tariffs get framed through Pembrokeshire exporters.
It’s not dilution. It’s amplification. In an era when readers can access global news with a swipe, the Herald’s edge is showing why it matters here—in Fishguard, in Tenby, in Milford Haven.
Echoes in the community
Beyond clicks and rivalries, the Herald’s impact is measured in voices amplified and lives touched.
It campaigned against the digital divide for Welsh speakers.
It investigated care home standards and planning controversies that spurred petitions.
It exposed scams targeting pensioners, warning thousands before more damage was done.
In a county where business survival rates are half the Welsh average, its coverage of grants, investments, and community projects kept people informed about lifelines.

“Without the Herald, I’d never have known about the funding that helped me save my shop,” says a Tenby café owner.
And when Pembrokeshire’s small producers — from vineyards to leatherworkers — took their products to Westminster, the Herald was there to capture it. MP Henry Tufnell later remarked that its stories “drive innovation and prosperity,” showing the paper’s role in amplifying the rural economy.
Even social media tells the tale. The Pembrokeshire Vikings rugby team thanked the Herald for sponsoring a player’s birthday celebration. The Welsh Organic Tannery posted “Diolch” for Herald photos of their Christmas Fair success. And PR agencies regularly highlight Herald stories as proof of local buzz. In an age of fleeting feeds, those simple thank-yous show a deeper truth: the community sees the Herald not just as a newspaper, but as a neighbour.

Lessons and the road ahead
Twelve years on, the Herald stands as proof that local news can adapt. From its scrappy print launch to its free digital empire, it has shown survival is possible—even in the harshest climate.
But the questions remain:
- Can the free model sustain itself long-term?
- Will more partnerships with the BBC or AI-driven alerts keep it ahead?
- Could its blueprint be copied in other rural counties starved of news?
For now, Sinclair is reflective but resolute. “We’ve shown local news isn’t dying—it’s adapting. From print rebels to digital warriors, we’ve kept Pembrokeshire’s pulse beating.”
The Irish Sea still pounds Pembrokeshire’s cliffs. Sheep still outnumber people. But thanks to one rogue wave of a newspaper, the county’s stories are louder, sharper, and freer than ever.

Features
Five exclusive interior design trends for upscale home makeovers

A recent Rightmove House Price Index suggests only modest movements in the UK housing market through spring 2024.
This is a time of year when prices typically soar, so this might lead many to consider revamping their current home for a touch of luxury rather than embarking on a stressful move.
After all, your existing space holds memories and character. But how can you elevate it to feel truly high-end? Let’s look at ways to transform your home into a luxurious haven.
Smart Home Integration
Luxury goes beyond aesthetics; it’s about creating a home that anticipates your needs. Smart home technology is no longer a vision of the future – it’s now easily accessible. Integrate voice-controlled lighting, automated blinds, and a zoned heating system controlled by your phone. Imagine walking into a perfectly lit room with the ideal temperature already set – that’s the epitome of effortless luxury.
Sophisticated Lighting
Lighting is essential for creating the ambiance of a space. Move away from harsh overhead lights and embrace a multi-layered approach. Think dimmable spotlights for task lighting, strategically placed sconces for a warm glow, and LED strips to create a touch of drama along walkways. Consider incorporating smart lighting systems that allow you to adjust colour temperature and intensity based on the time of day or desired atmosphere.
Enhance Your Hallway
First impressions matter, and your hallway sets the tone for the rest of your home. Don’t let it be a neglected space. Invest in a statement piece of art, a luxurious rug, or a stylish console table. Utilise the often overlooked understairs space. Here, bespoke joinery can create hidden storage solutions for coats, shoes, or even a mini home office.
Luxury Outdoor Spaces
With the rise of “staycations,” gardens and patios are no longer afterthoughts. Blur the lines between indoor and outdoor living by creating a luxurious extension of your home. Invest in comfortable outdoor furniture, weatherproof cushions, and stylish fire pits for cooler evenings. String fairy lights or install statement pendant lamps for a touch of magic after dark.
Customised Home Libraries
A well-designed home library isn’t just for bibliophiles; it’s a sophisticated and inviting space for relaxation and contemplation. Built-in bookshelves that maximise wall space are ideal. Consider incorporating a comfortable reading nook with plush armchairs and a statement lamp. For a truly unique touch, explore custom-built options that can accommodate your specific needs and showcase your treasured book collection.
Sustainable Design Adds Luxury
Luxury can be achieved without compromising the environment. Look for furniture and materials made from recycled or sustainable sources. Invest in energy-efficient smart home technology and consider installing skylights to take advantage of natural light.
By integrating these exclusive trends, you can turn your home into a space that showcases your unique style and personality. Remember, luxury is about creating something that feels effortlessly comfortable and perfectly suited to your lifestyle.
-

 Health6 days ago
Health6 days agoWelsh Ambulance Service to host bi-monthly Board meeting
-

 News5 days ago
News5 days agoRayner and Lammy visit Wales to discuss justice and community safety
-

 News4 days ago
News4 days agoFishguard linked to allegations in Many Tears Animal Rescue investigation
-

 News2 days ago
News2 days agoEmergency services flood Haverfordwest after reports of person in river
-

 News7 days ago
News7 days agoCalls grow for water industry overhaul after Welsh Water faces £44.7m fine
-

 Education7 days ago
Education7 days agoManorbier school closure approved while insurance claim still unresolved
-

 Charity6 days ago
Charity6 days agoMany Tears Animal Rescue visited by inspectors as police attend in support role
-

 Farming7 days ago
Farming7 days agoFarmers’ Union warns proposed lamb welfare changes risk unintended consequences